We spotted an unusual phishing email which revealed a new scam your users will soon find in their inbox. Time to inoculate them before it becomes a problem!
Many online service providers like Microsoft, Google, Facebook, Twitter, and PayPal have adopted a policy to warn users via email when there is a possible security-related event like "unusual sign-in activity".
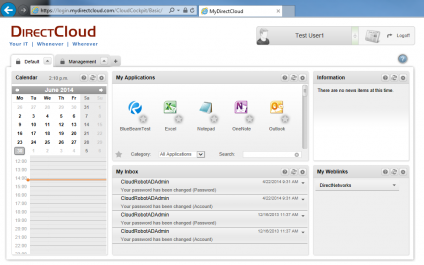
Copies of these emails have been used for credentials phishing for a few years, but the problem is these security notifications are now being used by bad guys as a new attack vector for a tech support scam.